Blog 1: Understanding TLPT before the clock starts ticking
📋 For the boardroom DORA requires financial institutions to conduct a Threat-Led Penetration Test (TLPT) every three years. This is not a standard security audit: it is a full-scale simulation of a real cyberattack on your critical systems, executed by professional attackers against your live environment. The process takes approximately nine months and typically costs between €100,000 and €150,000. The good news: you have time to prepare properly. The bad news: most organizations waste that time. This blog series explains how not to.
Introduction
Most financial institutions that fall under DORA will need to conduct their first Threat-Led Penetration Test within the next few years.
Most of them are not ready.
Not because they lack security, many have solid defenses in place. But because a TLPT is not a test you pass by having good security. It is a test you pass by understanding your own organization deeply enough to let real attackers try to break it, under controlled conditions, with real consequences if you are not prepared for what they find.
We have been executing red teaming assessments for over a decade. We have seen organizations walk into TLPT processes completely unprepared, spend nine months in reactive mode, and come out the other end with a report full of findings they do not know what to do with. We have also seen organizations that treated the years before their TLPT as an opportunity, and those organizations get dramatically more value from the process.
This series is for the second group. Over the past decade, we have guided organizations through red teaming assessments of every shape and size. We know what separates a TLPT that produces real change from one that produces a filed report. Our aim with this series is straightforward: to give you the insight and tools to be in the first category.
In this first post, we cover:
- What a TLPT is and how it actually works
- The TIBER-EU framework that underpins it
- How a TLPT differs from regular red teaming, and why that distinction matters
- Why you have more time than you think, and how not to waste it
What is a Threat-Led Penetration Test?
A Threat-Led Penetration Test is a regulated, intelligence-driven red team exercise. The key word is intelligence-driven.
Unlike a standard penetration test, where testers look for vulnerabilities across a defined scope, a TLPT starts by identifying the threat actors, the specific groups and individuals most likely to target your organization, how they operate, and what they are after.
But before threat intelligence shapes anything, you need to understand your own organization deeply enough to define what actually matters. Which functions are critical to your operations? Which systems underpin them? What would a meaningful compromise look like? Those answers form the foundation of the test. The threat intelligence is then gathered around those critical functions, identifying the threat actors most likely to target them and the techniques they use. From there, the attack scenarios follow.
The result is a test that does not ask "can someone break in?" It asks "can the specific type of adversary most likely to target us break in, and if they do, will we notice, and if we do, will we respond effectively?"
That is a fundamentally harder question. And a far more valuable one.
The TIBER-EU framework
DORA mandates that TLPTs follow a regulated framework. The framework was originally developed as TIBER-NL by the Dutch National Bank (DNB), before being adopted and further developed at European level as TIBER-EU by the ECB. TIBER-EU stands for Threat Intelligence Based Ethical Red-Teaming. The ECB has updated the TIBER-EU framework to fully align it with DORA's specifications for TLPT. TIBER-EU is the most widely adopted framework for meeting those requirements, and in practice the de facto standard. Technically, other frameworks that meet the same specifications could qualify, but given the prevalence and regulatory recognition of TIBER-EU, alternatives remain exceptional.

The framework defines three phases:
- Preparation: scope is defined, providers are selected, and the Generic Threat Landscape (GTL) report, produced by DNB and provided to the TIP, is used as input for the scoping process
- Test: Targeted Threat Intelligence is gathered based on the critical functions, attack scenarios are developed, and the Red Team executes those scenarios against your live environment
- Learning and Closure: findings are documented in the Red Team Test Report, a Replay and Purple Teaming session is conducted where Red Team and Blue Team jointly analyze what happened, a 360 feedback session takes place with all involved teams, and conclusions are discussed at board level and translated into concrete next steps
From start to finish, a TLPT process takes approximately nine months. That is not inefficiency: that is what a rigorous, intelligence-led test requires.
Who is involved?
TIBER-EU is deliberately designed to test how your organization responds to a real attack, which means most of your organization cannot know it is happening. In practice, these are the key roles:

The Control Team dynamic is worth pausing on. The head of the Blue Team is part of the Control Team, but the analysts and engineers in the trenches are not. They will face the Red Team without knowing it is a test. That distinction matters: it keeps the governance and escalation lines intact, while ensuring that the operational response is genuine. If your Blue Team detects and responds effectively under those conditions, you have learned something real. If they do not, you have learned something even more valuable.
One decision you will need to make early: whether to use the same provider for both the TIP and RTT roles, or separate parties. Both are permitted under TIBER-EU, but the choice has implications for the quality and independence of your threat intelligence. We will come back to this in detail in Blog 3.
How a TLPT differs from regular red teaming
Red teaming is a broad category. There are scenario-based tests, assumed breach exercises, Advanced Red Teaming (ART) assessments, and more. A TIBER-EU test sits at the more demanding end of that spectrum. Three things make it distinct:
1. Mandatory threat intelligence A dedicated Targeted Threat Intelligence Report is produced by the TIP. It identifies the threat actors most relevant to your organization, not generic attacker profiles, but the actual groups and techniques most likely to target your sector and business model. This report drives every decision that follows, including which scenarios are developed and executed.
2. A structured scenario selection process Based on the threat intelligence, the TIP develops a shortlist of scenarios executed by the threat actors most relevant to your organization and with the highest learning value. For organisations that have completed multiple TLPT cycles, repeating the most severe scenarios without variation adds little new insight. Relevance and learning value are the guiding criteria, not severity alone.
3. Regulatory oversight The Test Manager, appointed by the relevant authority, is involved throughout. This is not a test you can shortcut or scope down for convenience. Completing a TIBER-EU test in full compliance with the framework results in an official attestation: confirmation that you have met your DORA TLPT obligations.
These requirements mean that a TIBER-EU test produces something a standard red team engagement cannot: a regulated, documented assessment that satisfies your supervisor and gives you genuine insight into your resilience, not just a list of vulnerabilities.
How each scenario unfolds: the Unified Kill Chain
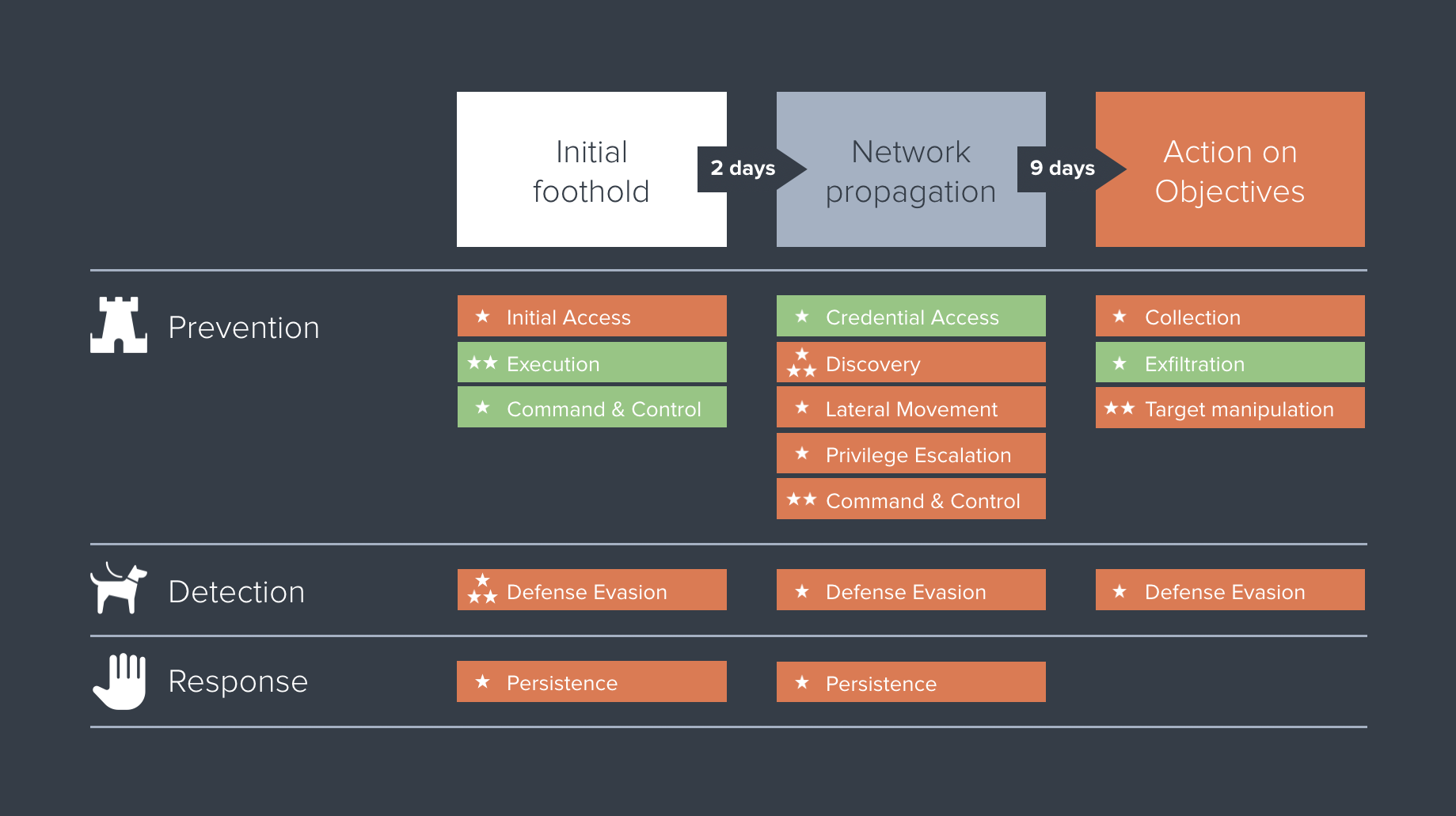
Each scenario follows the Unified Kill Chain, a model that maps the sequence of actions a real attacker takes from first contact to final objective. It has three phases:
IN: Initial Foothold The attacker identifies entry points and attempts to gain access. This is rarely just a technical exercise. Targeted phishing campaigns against employees with privileged access, exploitation of a public-facing application, credential theft via a compromised supplier, and yes, physical intrusion into office environments or data centers, are all realistic and legitimate IN-phase techniques. The threat intelligence report determines which approaches are most relevant to your specific threat profile.
THROUGH: Network Propagation Using legitimate credentials and tools, the attacker moves through your environment, escalating privileges, establishing persistent access, avoiding detection, and working toward the target. This phase often exposes the gap between what your security tools can detect and what your team actually catches in practice, and equally important, how they respond when they do detect something. Detection without effective response is not resilience.
OUT: Action on Objectives The attacker achieves their goal. Data exfiltration. Disruption of a critical process. Unauthorized access to sensitive systems or data. What that objective looks like depends entirely on the threat intelligence, which is why it is so important to get that intelligence right.
Scenarios typically follow the full attack chain, from initial access to achieving the attacker's objective. However, with approval from the Test Manager, a scenario can start from an assumed compromise, for example a pre-established foothold in the environment. Budget and learning objectives both play a role in that decision.
The scenario plays out in your live environment, against your real defenses, with your real team responding, without knowing it is a test. That is what makes it hard. And that is what makes it useful.
Key benefits: beyond regulatory compliance
DORA compliance is a reason to do a TLPT. It is not the reason to do it well.
Organizations that treat TLPT purely as a compliance exercise consistently get less from it than organizations that approach it as a genuine resilience test. Done well, a TLPT gives you three things that no other test can:
A realistic picture of your actual resilience Not your theoretical security posture: your actual ability to withstand a sophisticated attack by a motivated adversary targeting your specific organization, using the techniques they actually use.
A measurable baseline A well-executed TLPT produces concrete, measurable data on your prevention, detection, and response capabilities. At Securify, we translate every red team engagement into a scorecard that gives you exact numbers across the full attack chain, so you can see precisely where your defenses held and where they did not.
That scorecard is what makes your next TLPT a meaningful comparison rather than a standalone exercise.
Organizational alignment A TLPT forces a structured conversation between your security team, your board, and your regulators about what your critical assets actually are, what the realistic threats to those assets look like, and what you are prepared to invest in protecting them. That conversation is valuable regardless of what the test finds.
Why you have more time than you think, and why that matters
DORA requires a TLPT every three years. The test itself takes approximately nine months. That leaves over two years of runway before you need to start the TLPT process.
Most organizations treat that runway as waiting time.
That is a mistake.
The organizations that get the most from their TLPT are the ones that used the pre-TLPT period intentionally: running targeted security tests, fixing structural vulnerabilities, and building their team's capacity to detect and respond to attacks. By the time the TLPT started, the low-hanging fruit was gone. The test was harder for the Red Team. The Blue Team performed better. And the findings were more strategic, not "you have unpatched external systems" but "here is exactly how a sophisticated attacker would navigate your specific environment."
That is the difference between a TLPT that produces a remediation backlog and a TLPT that produces strategic insight.
In our next blog, we will show you exactly how to build a security testing strategy that prepares your organization for TLPT, and delivers real security improvements in the process.
In short
A TLPT is not a bigger, more expensive penetration test. It is a structured, intelligence-driven simulation of a real attack on your organization: regulated, rigorous, and revealing in ways that standard tests are not.
If you fall under DORA, you will need to do one. The question is whether you will be ready when it starts, or whether you will spend nine months finding out how unprepared you were.
The next two years are your opportunity. Use them.
In Blog 2, we walk through the pre-preparation phase: how to build a security testing strategy that gets your organization TLPT-ready, and what that looks like in practice.